Recent Guidance from the PCI Council

One would think that the publication of the next version of the PCI DSS (April 2016) as well as the sunset date of the previous version (in October 2016) would constitute a pretty full year for PCI. However, the end of 2016 and beginning of 2017 saw a flurry of activity from the PCI Security Standards Council (PCI SSC), specifically around their Guidance Documents.
The following Information Supplements were published in the last year:
- Assessment Guidance for Non-Listed Encryption Solutions (November 2016)
- Guidance for PCI DSS Scoping and Network Segmentation (December 2016 & May 2017)
- Multi-Factor Authentication (February 2017)
- Best Practices for Securing E-commerce (April 2017)
While there is too much detail in each document to cover everything here, I’ve tried to summarize the information provided by each document and add any commentary that may help you understand the details in each supplement.
Continue Reading "Recent Guidance from the PCI Council" (a 14 minute read) >
Evolving NIST Password Guidance and PCI

Passwords are difficult. They have to be a certain length, use certain characters, change at certain intervals, and worst of all they have to be memorable. But the NIST Trusted Identities Group thinks that should change.
The new draft version of NIST’s Digital Identity Guidelines (SP 800-63-3) is in the process of being finalized. The sub-publication on Authentication & Lifecycle Management (800-63b) contains some interesting changes to password composition and management. The document uses the term “memorized secrets” to refer to passwords and PINs. Also, as this is still a DRAFT version, it is advisable to wait for the final publication to refer to before changing security policies.
Continue Reading "Evolving NIST Password Guidance and PCI" (a 3 minute read) >
ShmooCon 2017

Urbane Java
At ShmooCon? Join us upstairs at Suite 2101 for our pop-up coffee bar on Friday, Saturday, and Sunday.
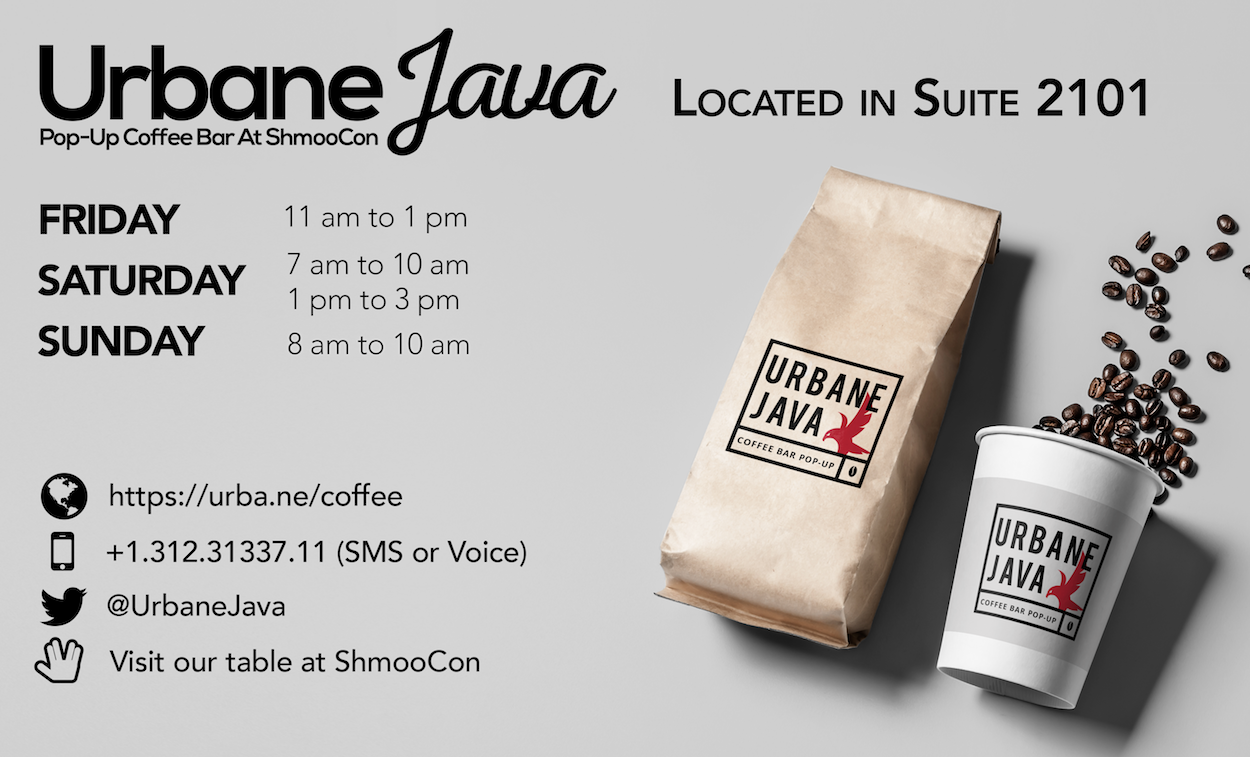
Test Your Skill
Join us at the Urbane table for a heated 4 player head to head game of Simon. High scores each day will win great prizes. Find your Urbane Gaming Card in your ShmooCon bag and head on over!
Get Out And Vote!
Election Night, 2016
A vote for anyone is a vote for the EFF
This election day, we celebrate in the US our freedom and democratic process. Fighting for our freedom in the digital space are our friends at the Electronic Frontier Foundation (EFF.org). That’s why this election day, Urbane will donate $1 to the EFF for each person who tweets their “I Voted” sticker (or like evidence) with the hashtag #InfosecVotes.
Unlike your Facebook friends, we’re not here to judge you for voting for Hillary, Trump, Johnson, Stein, or your write in for John Stewart. Vote for your President. Vote for your Senators and Representatives. Vote for your local issues. Whether you’re left, right, in the middle, or off the spectrum, your vote is your voice, and a vote for anyone this week is a vote for the EFF.
And now, a few notes about this drive.
Urbane Security will donate $1 per verifiable individual (sorry Twitter botnets of toasters and tea kettles) to the Electronic Frontier Foundation up to USD $5000 with the hashtag #InfosecVotes along with an “I Voted” sticker or similar proof of vote. Your tweet and picture must be posted by November 9th at 23:59 Eastern Time.
Trick or Treet - ShmooCon 2016 Edition

Urbane is once again sponsoring ShmooCon this upcoming year, and we have a number of ShmooCon tickets to give away before registration even opens! That’s right, this is your chance to secure a ShmooCon ticket without having to race to solve the captcha faster than anyone else.
Continue Reading "Trick or Treet - ShmooCon 2016 Edition" (a 2 minute read) >
